Learn to write great code through immersive hands-on classes.
Sharpen your skills with programming competitions & hackathons.
Create, compete, collaborate, and code the world a better place.
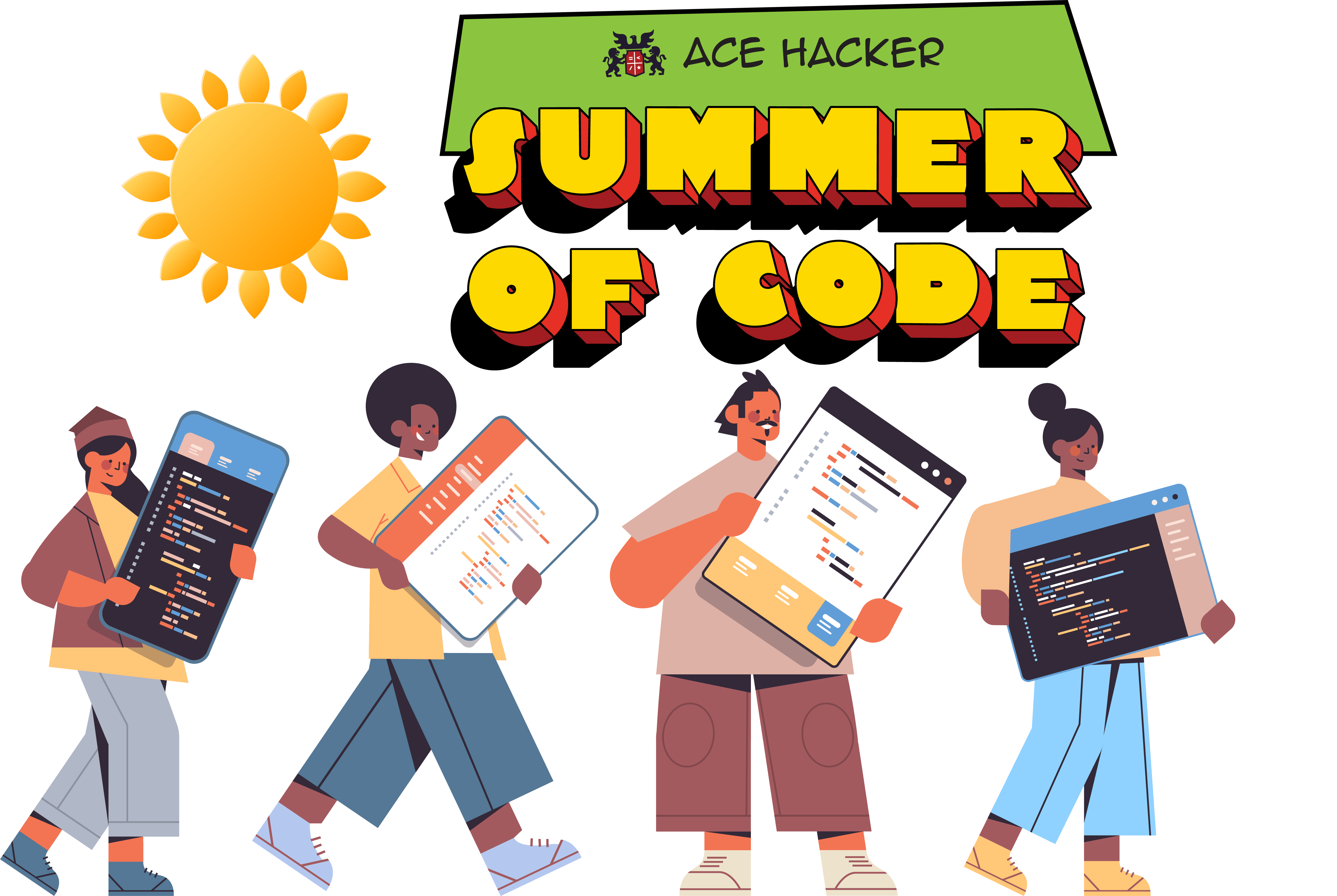
Summer of Code.
Mar 15th - Jun 14th
Dive into the magical world of programming! Whether you’re 12 or 102, this summer we’re turning curious minds into code wizards with our wildly fun, beginner-friendly Python course. No prior experience? No problem. Just bring your excitement - we’ll handle the rest. Let’s make this a summer worth debugging.
This is an instructor-led course. Ask questions, get real-time help, and interact with your trainer in a real class. We like to keep things cozy - just 25 students max per class. That means more questions, more answers, more laughs, and way more “Aha!” moments.
Explore Python for BeginnersExplore all courses →
Code Your Stories.
Ace Hacker courses are crafted to convey the most complex concepts through engaging stories. Tinker with the code in every story, and push boundaries without fear of failure. Build meaningful solutions to tackle real-world problems. Have fun along the way.
Competitions.
Hack that code. Enhance your skills by participating in sprint programming competitions or marathon hackathons. Compete for bragging rights. How does this work?
Take the Quantum Leap!
Step into the strange, exciting, and mind-bending world where bits can be both 0 and 1 at the same time, particles share secrets across galaxies, and measurements change reality itself.
In this course, you won’t just learn about quantum computing - you’ll play with it. From mastering the concepts of superposition, entanglement, and measurement to actually running experiments on IBM’s real quantum computers, you’ll be doing science that was sci-fi just a decade ago. Whether you’re an innovator, problem-solver, or just quantum-curious, this is your chance to future-proof your skills and join the computing revolution that’s rewriting the rules of possibility.
Explore Quantum ComputingExplore all courses →
Seasons of Code.
At Ace Hacker, there’s always a season of code. We celebrate the year round with fresh themes and new adventures in tech - each season bringing it’s own unique flavour to learning and competition.
From the creative spark of Spring to the deep mastery of Winter, every season invites learners to dive into coding, explore updated topics, experiment with ideas, compete with peers, and collaborate on projects. Whether it’s building, breaking, or reinventing, we believe code is worth celebrating in every season.
Spring of Startups.
Feb 15th - Mar 14th
Spring of Startups is when innovation blossoms at Ace Hacker. Each year, the Ace Hacker Accelerator - Hackceler8 opens its doors, inviting deep tech startups to apply and be part of something extraordinary. From the many applicants, 8 startups across 8 focus areas are chosen to join the Hackceler8 cohort that kicks off every April.
It’s the season of fresh beginnings, bold ideas, and startups accelerating toward their next big leap.
Know more about Hackceler8
No Code Monsoons.
Jun 15th - Sept 14th
This monsoon, dive into the world of AI & ML without breaking a sweat - or writing a single line of code. This course is your fast-track to understanding the tech that’s reshaping industries, helping you talk the talk with your geeky team. We’ll break down complex concepts into bite-sized, immersive & engaging lessons, so you can confidently lead your organization into the AI-powered future. No coding, just pure insight and a sprinkle of fun.
It’s live. It’s instructor-led. It’s human. Ask questions, get instant clarity, and share laughs with a real expert and a small class of 25 students max.
Decode AI & ML without CodeExplore all courses →
Autumn of Algorithms.
Sept 15th - Nov 14th
This Autumn, the Land of AL needs a hero. Sharpen your skills in Data Structures & Algorithms through an epic, story-driven quest with the legendary Wizard of AL.
As the leaves turn golden and the air grows crisp, it’s the perfect time to gather your wits, hone your skills, and prepare for challenges ahead. This Autumn, the fabled Land of AL calls out to brave learners - a place where Data Structures and Algorithms are not just lessons, but the lifeblood of a magical realm. Solve challenges. Cast algorithmic spells. Become the coder you were meant to be.
Explore Data Structures & AlgorithmsExplore other courses →
Winter of Web.
Nov 15th - Feb 14th
When the world outside chills, the web heats up at Ace Hacker. In this immersive, project-driven adventure, learners become full-stack creators - crafting sleek frontends with HTML, CSS, and JavaScript, then powering them with the mighty MERN stack (MongoDB, Express.js, React, Node.js).
Every project is a snowflake - unique, challenging, and beautiful - pushing you closer to mastering the art of Full Stack Web Development. By the end of Winter, you won’t just browse the web - you’ll build it.
Explore Full Stack Web DevelopmentExplore other courses →